How Wi-Fi router security has deteriorated since 2003

WASHINGTON, D.C.—Your home Wi-Fi router, your neighbor’s Wi-Fi router, your favorite coffee shop’s Wi-Fi router, and your employer’s Wi-Fi router are all far more vulnerable to hackers now than they were 15 years ago.
The Cyber Independent Testing Lab, a nonprofit organization that focuses on consumer cybersecurity, published research in December demonstrating how 28 home wireless routers fail to use even basic security techniques. And at the annual hacker conference ShmooCon on Saturday, CITL presented an update to that research, showing identical or similar weaknesses in 1,000 home and commercial Wi-Fi routers, across 6,000 firmware versions and 18 vendors, including highly rated devices from brands such as Asus, Belkin, Buffalo, D-Link, Linksys, and Netgear.

Of those vendors, only D-Link responded to requests for comment.
“D-Link has promptly started investigating the issue, and we will provide updates as soon as we have more information,” company representative Michelle Chiang said in an email. “D-Link takes the issues of network security and user privacy very seriously.”
It’s no secret that many Wi-Fi routers are highly insecure. Security researchers, pointing at issues such as hard-coded default passwords and irregular security updates, have been issuing warnings for years. What might be alarming about CITL’s latest research is that despite the alarm bells, CITL finds that vendors are generally building Wi-Fi routers with fewer protections than they had in 2003. The organization’s acting director, Tim Carstens, says the research will be published soon on the CITL site.
READ MORE ON WI-FI SECURITY
- FBI’s router reboot call reminds us why to check for updates
- Your old router could be a hacking group’s APT pawn
- Why hackers love your Wi-Fi (and how to protect it)
- How to secure your home Wi-Fi
- Time for a Department of the Internet of Things?
- The long reach of Mirai, the Internet of Things botnet
The struggle to secure routers “may be the challenge of our current times,” Carstens told a conference audience.
During a conversation with The Parallax after the presentation, Carstens declined to speculate as to why router vendors are building less-secure routers, except to say that they may not have closely tracked how their own firmware code has changed over the years.
“Vendors don’t have a system for testing, checking, and verifying that hardening features they believe to be turned on, and sometimes were, are still present,” CITL lead researcher Parker Thompson said from the SchmooCon stage. “This is effectively an iceberg.”
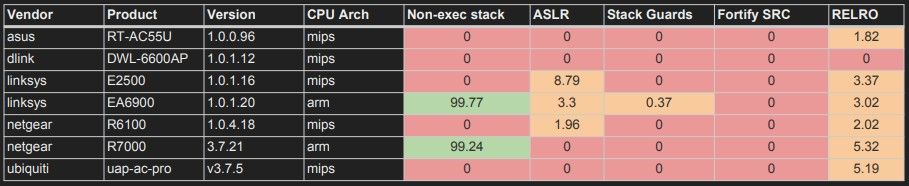
Most router firmware today fails to use basic security-hardening techniques considered standard for software and device firmware, Carstens says, such as Address Space Layout Randomization (ASLR), first used in 2001, data execution prevention (DEP, 2004), correct ordering and marking of segments in the binary to prevent overwriting jump-tables for Linux systems (RELRO, 2004), fortify source code (2005), and stack canaries to thwart stack overwrites (Stack Guards, 1997).
CITL says its research shows that such important security-hardening features are either nonexistent on modern routers, or are present only rarely and inconsistently. Worse, CITL argues that in analyzing router firmware security, it discovered that most router firmware has lost hardening features over time, including a notable decrease in the use of ASLR.
That means that while some routers may force consumers to change the default password when setting up the device, which they probably didn’t do 5 or 10 years ago, the security built into the software itself to prevent exploitation has been weakened over the same period.
The majority of today’s popular Wi-Fi routers run the Linux operating system (which also powers Google’s Android) with MIPS processors. CITL first detailed a major vulnerability in Linux with MIPS in a report it published alongside its December report on routers. One example Thompson cited on Saturday was D-Link’s DAP-2690 Wi-Fi router. ASLR was part of the router’s built-in security from its debut in 2011, but it disappeared toward the end of 2016, when the Linux MIPS code was updated to version 4.8.
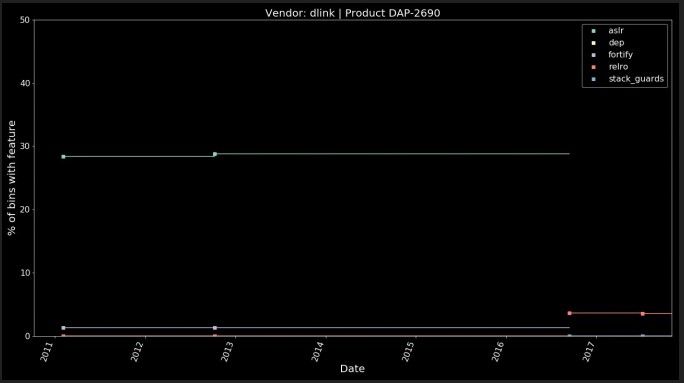
Thompson says CITL’s research concludes that the downgrade wasn’t a rare event. All major router vendors shipped fewer routers with firmware sporting ASLR protections in 2018 than in 2012, he said.
Firmware is software designed to control hardware devices ranging from routers to Internet-connected door locks to baby monitors to personal assistants. And importantly, the Wi-Fi router—long considered a connectivity hub for laptops and phones—has become the home connection point for the so-called Internet of Things.
As Internet-connected devices have proliferated, security experts have stepped up pressure on vendors to improve IoT security. Yet even today’s most secure devices are regularly connecting with routers, which CITL finds not only are generally lacking standard protections but have become progressively less secure.
Renowned network security expert Peiter “Mudge” Zatko, who co-founded CITL and serves as chairman of its board, said at the end of the presentation that his organization’s research needs to be taken seriously not just by home consumers but by “anybody who is acquiring for an organization or agency or business” because it’s based on “actual data,” not just on “what feels secure.”
“There is a dearth of quantified data in [the cybersecurity] community,” he said. “There’s a lot of low-hanging fruit. What we’re finding is that when we do look for the actual data underneath, the advice and groupthink is wrong.”
Because of vulnerabilities introduced into Linux MIPS in 2016, Thompson said, the architecture has become less secure by default and harder to secure.
“Now we have a generic DEP and ASLR bypass in every single Linux user space process on Linux MIPS,” Thompson said. “Linux MIPS has been missing fundamental hardening features for its entire lifetime, and with 2016 in 4.8 and above, it got worse. There’s just no safe version of Linux MIPS.”
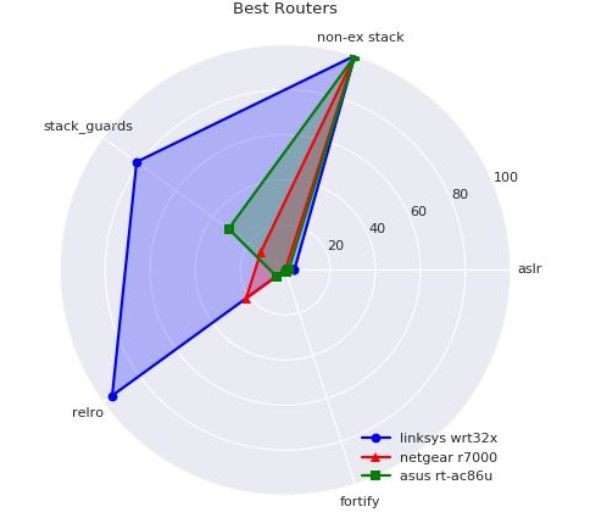
One router CITL recently tested, the Linksys WRT32X, outperformed others on the security front because more of its software components include more standard security features, such as RELRO and DEP. It also uses the ARM architecture instead of MIPS, but it is still lacking in security basics such as ASLR and fortified source code, Carstens says.
“Once an attacker has an exploit, they’ve pwned it,” he says.
