Congressmen at DefCon: Please help us, hackers!
LAS VEGAS—For the first time in the 25 years of the world’s largest hacker convention, DefCon, two sitting U.S. Congressmen trekked here from Washington, D.C., to discuss their cybersecurity expertise on stage.
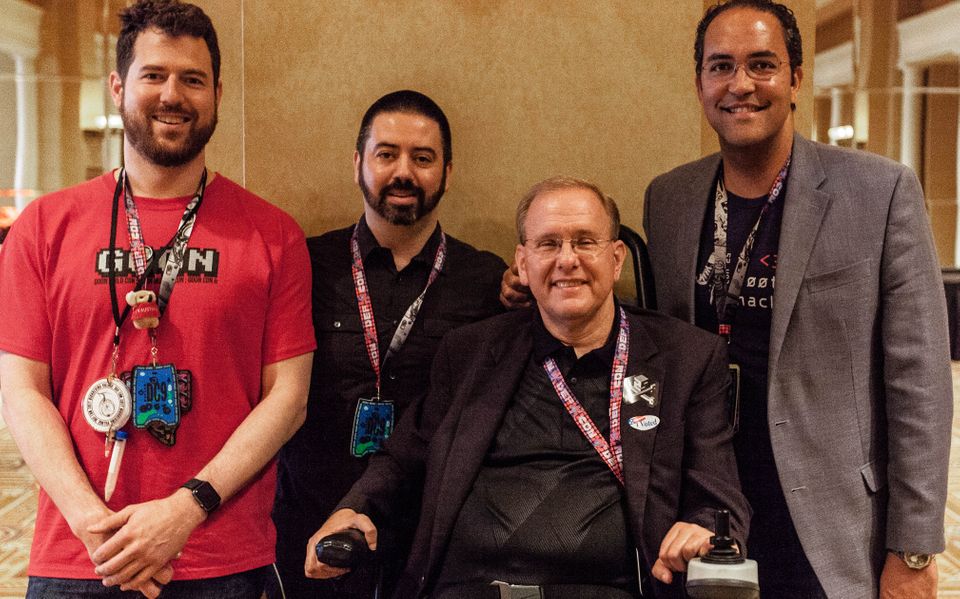
Rep. Will Hurd, a Texas Republican, and Rep. Jim Langevin, a Rhode Island Democrat, visited hacking villages investigating vulnerabilities in cars, medical devices, and voting machines; learned about how security researchers plan to defend quantum computers from hacks; and met children learning how to hack for good.
On Sunday, the last day of the conference, Hurd and Langevin delivered their own message: We come in peace. Please help us.
During a fireside chat-style conversation moderated by Joshua Corman, director of the Cyber Statecraft Initiative at the Atlantic Council, Hurd, chairman of the House Subcommittee on Information Technology, and Langevin, co-founder and co-chair of the Congressional Cybersecurity Caucus, called for the more than 2,000 hackers in the audience to “develop a dialogue” with their local representative in Congress.
“Never underestimate the value that you can bring to the table in helping to educate members and staff of what the best policies are, what’s going to work, and what’s not going to work,” Langevin said, pointing to Luta Security CEO and bug bounty expert Katie Moussouris’ ongoing advocacy for changes to the Wassenaar Arrangement, a decades-old international accord on how countries can transport “intrusion software” and other weapons across international borders.
Moussouris and Iain Mulholland of VMware have effectively convinced Wassenaar member countries to delay their adoption of proposed revisions to the agreement, as they’ve pushed for new language to better protect security researchers’ work.
The conversation between hackers and Congress has never been monosyllabic. But it has been frosty for decades, as federal prosecutors have used American antihacking laws such as the Computer Fraud and Abuse Act and Electronic Communication Privacy Act to punish people conducting legitimate security research.
As many security researchers continue to worry about how these laws might affect them, some have begun to use their expertise to influence the laws—and the lawmakers behind them.
Langevin and Hurd’s plea for hacker-legislator collaboration follows calls by hackers at last year’s DefCon for greater government regulation of software security.
“We don’t have voluntary minimum safety standards for cars; we have a mandatory minimum,” Corman told The Parallax at the time. “What tips the equation [for software] is the Internet of Things, because we now have bits and bytes meeting flesh and blood.”
Hurd said security researchers could play an important role in addressing increasingly alarming vulnerabilities in the nation’s voting apparatus. DefCon’s first voting machine-hacking village this weekend hosted a voting machine from Shelby County, Tenn., that unexpectedly contained personal information related to more than 650,000 voters. Village visitors managed to hack the machine, along with 19 others.
“We have to ensure that the American people can trust the vote-tabulating process,” Hurd said, acknowledging that DefCon attendees were able to hack each machine in the village. “The work that has been done out here is important in educating the secretaries of state all around the country, as well as the election administrators,” about secure technologies and practices.
Langevin and Hurd’s comments seemed to strike the right notes with hackers in attendance. Following Edward Snowden’s leaking of NSA documents and Apple’s refusal to create an encryption backdoor for law enforcement to the iPhone, relations between the hacking community and Washington have been strained at best, notes Herb Lin, a computer security policy expert and research fellow at Stanford University’s Center for International Security and Cooperation. But markedly improving the relationship will require more than a plea for collaboration, he warns.
“It’s better than what’s happened in the past, which is both nothing and active hostility,” he says. “One act by itself is not a game changer.”
The chat ended with assurances of more action from both sides. Corman said he’d like to see members of Congress attend more hacker conferences, such as ShmooCon in Washington, and Hurd promised that he wouldn’t let his experiences this past weekend go to waste.
“These conversations are going to lead me to hold hearings on many of these topics in the subcommittee that I chair,” Hurd said.
Updated on August 12 to clarify the number of machines and models present in the EVM hacking village. There were 20 machines across five models.
